
Does your organization comply with laws and regulations?
Every organization must comply with laws and regulations. This poses a great challenge for organizations. Please read on to find out how you will pass business process audits with flying colors.
Regulatory burden and compliance
Organizations must comply with more and more laws and regulations. For instance, you must be able to demonstrate in audits that your organization complies with the General Data Protection Regulation (GPDR) and ISO27001. If an audit shows that your organization is insufficiently in control, this may lead to a fine from the Dutch Data Protection Authority, or, in the worst case, shutting down your business. Therefore, solving problematic audit findings is a high priority.
False security
Being able to demonstrate compliance with laws and regulations, and standards and requirements, is in many organizations a time-consuming, complex, and error-prone process. Fragmented information is often manually merged into one overview. This increases the risk of errors, and as an organization you have only limited control over this process, especially if this is only checked once a year. In addition to spending a lot of time, this also results in a certain degree of “false security”.
Do you want to achieve real security? This is what your organization should know:
- How do I deal structurally and as quickly as possible with problematic audit findings?
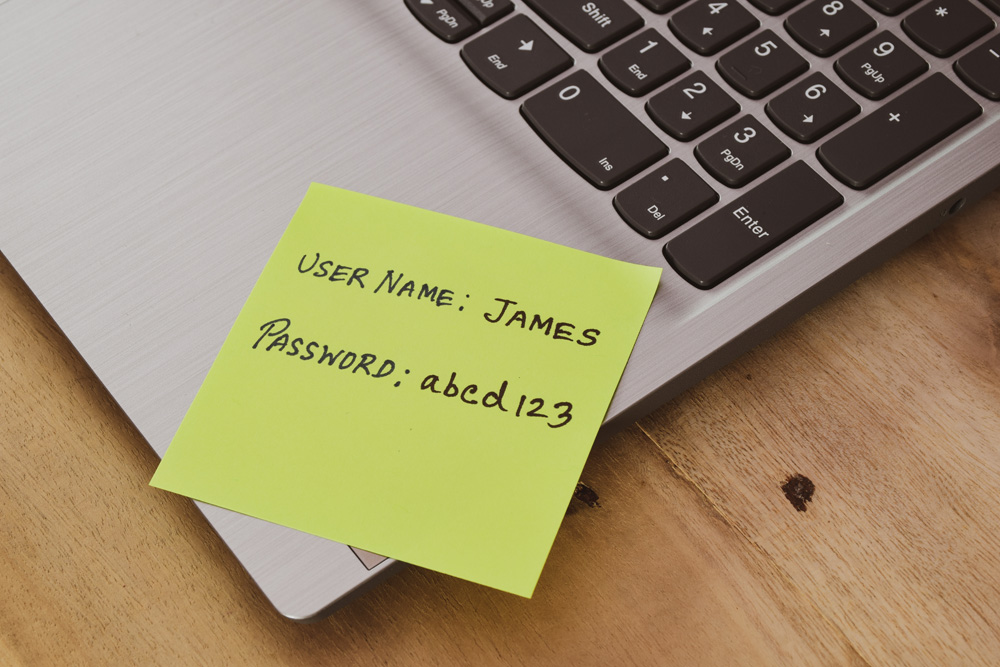
- Which identities have access to my company systems? And can this access be justified?
- Should I ask my customers for permission to store and use data, and what is the best way to do that?

Is your auditor satisfied?
A central system, in which information from the HR administration and access rights of identities in applications converge, enables you to demonstrate compliance with laws and regulations more efficiently and effectively to the auditor. This creates a complete overview of the rights that employees have. But it is more than just implementation of technology. It is also necessary to define duties and responsibilities.

If you do nothing
It may be tempting to use a “quick fix” to temporarily get rid of worrisome audit findings. But if your organization has only limited control, the risk of incidents increases. For that reason, data breaches by unauthorized access may become the order of the day. As a result, employees may be able to access privacy-sensitive data that they don’t need for the performance of their duties. This may not only have major financial implications, but also lead to reputational damage for your organization.
How to protect your company?
Your objective is to be able to demonstrate compliance with laws and regulations efficiently and effectively. But where do you start?
Achieving secured access
We will help you to reduce the risk of data breaches and to enhance your digital resilience by functionalities such as Multi-Factor Authentication (MFA), Risk-Based Access and Identity Proofing.
Mapping identities
We will help you to map the identities within your organization, decide where they should gain access to and which accounts to use for this purpose.
Compliance with privacy laws
We will support your organization in storing customer data safely and compliance with the most recent privacy laws.

How we can help you
It is very important to comply with laws and regulations. Not only because of audits, but most of all for the internal digital safety and securing the privacy of customers. We know from experience that many organizations, both large and small, don’t really know how to do this. We support and relieve your organization, from fine-tuning your objectives to implementing solutions and providing the desired level of support.

In conversation with NIBC
As a result of our IGA project, we have interviewed Steven Schulein, Head of Generic IT, in our Grabowsky Safe Zone. In the interview he will explain how he strengthened NIBC’s Identity & Access Management.

Do you want to boost your agility and resilience?
We would like to help you reach your goal by using the right Digital Identity strategy and suitable Identity & Access Management solutions for your employees, partners, suppliers and customers.
